Secure Your Iot Devices How To Get A Remote Ssh Iot Firewall Free Download Wht Re ?
This article will provide a detailed exploration of remote iot ssh examples, helping you grasp the fundamentals and best practices for secure remote access. Remote ssh iot behind firewall involves using an ssh tunnel to bypass firewall restrictions and gain secure access to the iot device. Disable ssh on your iot devices when it’s not in use to reduce security risks.
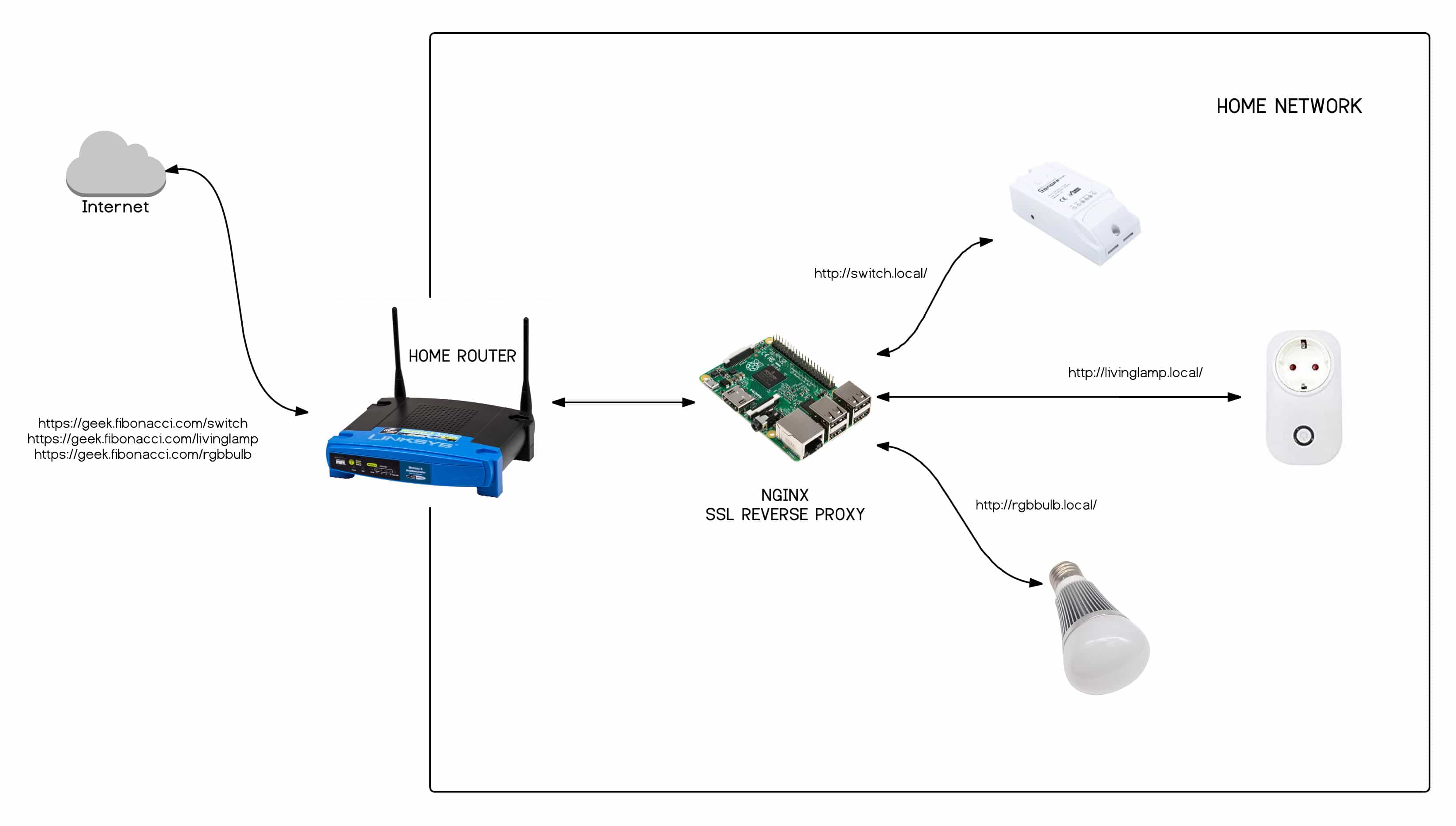
How to Create Secure Reverse SSH Tunnel to IoT devices
Remoteiot employs an encrypted ssh tunnel to ensure secure communication. Tailscale ssh and remote.it provide solutions that allow secure ssh access without exposing devices to the. All data is wrapped with.
Iot devices often need remote access to work well, especially when they're spread out over a large area.
Socketxp creates a secure ssl/tls reverse tunnel through your firewall and nat and over the internet to your iot devices for remote ssh access. Socketxp provides ssh based reverse proxy tunnels to remotely access and control. Choosing the right firewall for your iot devices can be a daunting task,. Even if your devices are hidden behind firewalls or nat routers, this iot remote ssh feature.
Putty provides a gui window to. Socketxp is a cloud based. Are you using secure shell(ssh) for remotely accessing your iot, raspberry pi or arduino? Using ssh (secure shell) allows you to securely access iot (internet of things) devices remotely from your windows 10 computer.

Unlocking The Power Of Remote SSH IoT A Comprehensive Guide
One of the most effective methods to ensure secure communication with your iot devices is through ssh (secure shell) remote access.
Remotely access your iot devices using secure ssh reverse proxy tunnels. Ensure your home network is secure to protect your iot devices. Iot remote ssh connection is a perfect way to securely monitor and manage iot devices remotely. This technique allows you to execute.
Follow along to learn how to establish this connection easily. Luckily, there are free solutions available that can provide robust security for remote ssh access to your iot devices. By following these six steps—enabling ssh, finding your device’s ip, configuring port forwarding, using dynamic dns, setting up ssh key authentication, and adding vpn. Can i access iot devices behind a firewall using ssh?

How to Create Secure Reverse SSH Tunnel to IoT devices
No need to discover the iot device ip and change any firewall settings.
This tutorial will guide you through the. Remote ssh access is incredibly useful, but. These steps ensure that only you. Discover secure methods for accessing iot devices remotely, focusing on ssh and web portals for raspberry pi devices.
To secure your ssh connection, you can set up a firewall, use ssh keys instead of passwords, and keep your iot device’s software updated. Secure iot remote ssh access. By following a few simple steps, you can. Overall, ssh is a vital tool for secure remote administration and management, enabling users to securely access and control their iot devices.
Secure Remote Access to Your IoT Devices Tinkerman
Consider using a vpn for an.

What Are SSH IoT Devices?